Most businesses still think cybersecurity is about installing antivirus and hoping nothing breaks. That approach no longer works. In 2026, attacks are faster, smarter, and often invisible until real damage is done. AI tools now allow attackers to automate phishing, mimic real voices, and scan vulnerabilities in seconds.
If you run a startup, agency, or small business, the risk is not theoretical. It is operational. One compromised login or API key can disrupt payments, leak customer data, or shut down systems entirely. This guide breaks down what is actually changing in cybersecurity and what practical steps you can take right now.
I. The AI Arms Race: Predictive Defense vs Automated Attacks
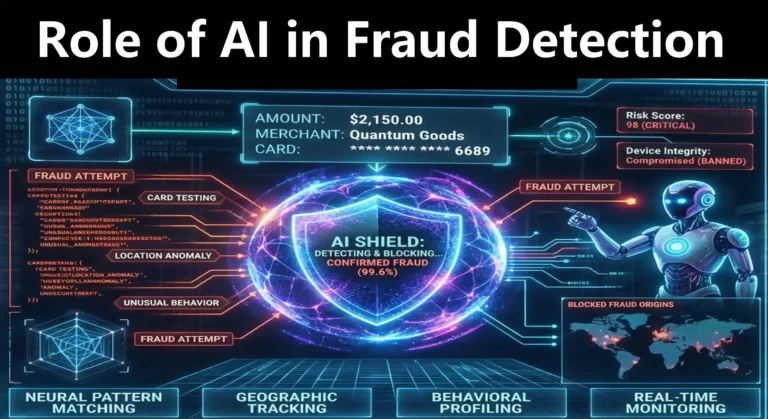
Cybersecurity has shifted from reactive protection to real-time prediction. Attackers use AI to test thousands of attack paths instantly. At the same time, defenders are using AI to detect unusual behavior before damage occurs.
From real-world observation, most breaches today follow a simple pattern:
- A weak login or leaked credential
- Automated scanning by bots
- Privilege escalation within minutes
This is why traditional monitoring fails. By the time a human reviews logs, the system is already compromised.
Global Cybersecurity Expenditure Forecast (2025-2027)
*Driven by AI security tools, cloud adoption, and compliance pressure*
What this means for you
You need systems that respond instantly, not tools that only alert you. AI-based detection tools that flag unusual login patterns or data access are no longer optional.
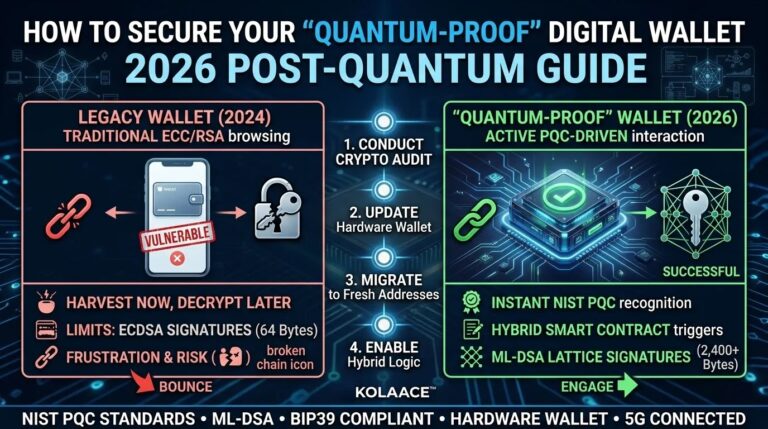
II. Post-Quantum Cryptography: Preparing Before It Is Too Late
Most businesses ignore encryption upgrades because current systems still work. That is a risky assumption. Attackers are already storing encrypted data today with the expectation that future quantum systems will decrypt it.
This is known as the harvest now, decrypt later strategy.
| Security Layer | Traditional Setup | 2026 Upgrade Approach |
|---|---|---|
| Identity | Passwords and OTP | Behavior-based authentication |
| Encryption | RSA and AES | Hybrid quantum-resistant algorithms |
| Monitoring | Manual review | Automated AI response systems |
Practical insight
If your business handles payments, customer data, or intellectual property, start planning crypto agility. This means your system should support switching encryption methods without rebuilding your entire infrastructure.
III. Identity Is Now the Main Attack Surface
Firewalls used to be the primary defense. Today, identity is the real perimeter. Attackers do not break systems, they log in.
- Deepfake fraud: Fake voice calls requesting urgent transfers
- API misuse: Automated systems accessing data silently
- Credential stuffing: Reused passwords across platforms
Real-world example
A small finance company approved a payment after receiving a voice call from what sounded like their CEO. It was a deepfake generated using publicly available audio clips. No malware was used. The system was technically secure, but identity verification failed.
Best practice
- Use multi-layer authentication beyond SMS
- Monitor login behavior, not just credentials
- Limit access based on role and necessity
IV. Step by Step Cybersecurity Upgrade Plan for SMEs
- Audit your current access
List who has access to what systems. Remove unnecessary permissions immediately. - Enable behavioral monitoring
Track login patterns, device usage, and unusual activity. - Adopt AI-based security tools
Use tools that automatically detect and respond to threats. - Prepare for encryption upgrades
Ensure your infrastructure can adapt to future standards. - Train your team
Most attacks still succeed due to human error. Awareness reduces risk significantly.
V. Pros and Cons of AI Driven Cybersecurity
Advantages
- Faster detection of threats
- Reduced manual workload
- Better prediction of attack patterns
Limitations
- Requires proper setup and tuning
- False positives can occur
- Over-reliance without human oversight can be risky
VI. Who Should Take Immediate Action
- Startups handling payments or user data
- Freelancers using multiple SaaS tools
- Ecommerce and digital service businesses
Who can take a gradual approach
- Offline businesses with minimal digital exposure
- Small teams using limited online systems
Conclusion
Cybersecurity in 2026 is defined by speed, identity, and adaptability. Waiting for an incident is the most expensive strategy. Businesses that invest in proactive systems, even at a basic level, are significantly more resilient.
Start small if needed, but start now. Even simple steps like tightening access control and enabling smarter monitoring can prevent major losses.