As we navigate the first quarter of 2026, the global banking sector has reached a critical “Y2Q” (Years to Quantum) milestone. KOLAACE™ has observed that the theoretical threat of quantum decryption has shifted into a practical, systemic risk for financial institutions. The primary catalyst? The release of the 1,121-qubit “Condor” class processors, which have brought us dangerously close to the 2,048-qubit threshold required to break standard RSA encryption.
This industry guide builds upon our earlier deep dive into quantum-resistant digital asset security (Post #38) and addresses the specific infrastructure pressures created by the 2026 shift to edge computing (Post #39).
The End of Mathematical “Trapdoors”: Why RSA and ECC are Failing
For over 40 years, global finance relied on the “hardness” of prime factorization. Classical computers find factoring large numbers nearly impossible, providing the “trapdoor” that secures your bank logins and wire transfers. However, Shor’s Algorithm, when run on a cryptographically relevant quantum computer (CRQC), solves these problems in polynomial time.
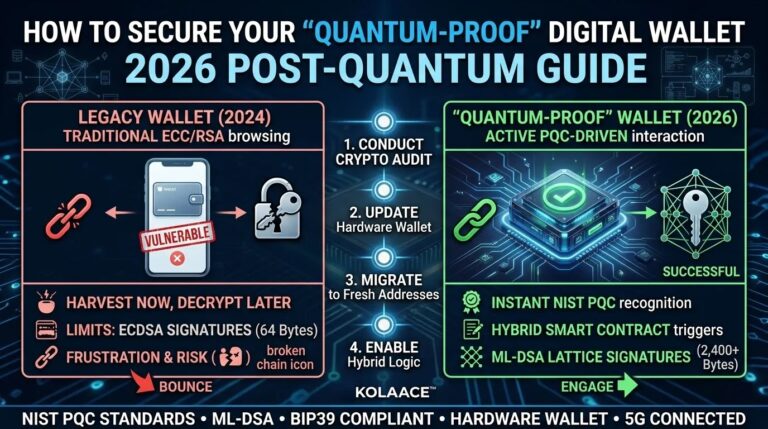
In 2026, the risk is no longer just “future decryption.” We are seeing the rise of “Harvest Now, Decrypt Later” (HNDL) attacks. Adversaries are intercepting and storing encrypted financial traffic today, waiting for quantum hardware to mature enough to unlock it. This makes immediate migration to NIST FIPS 203, 204, and 205 standards a survival requirement, not just a compliance checkbox.
KOLAACE™ Global Market Analytics: The PQC Adoption Curve
Our intelligence division has tracked the migration of Tier-1 banks to Post-Quantum Cryptography (PQC). The 2026 surge is driven by new mandates from the European Digital Operational Resilience Act (DORA) and the U.S. National Security Memorandum 10.
Tier-1 Bank Migration to Post-Quantum Standards
Data Source: KOLAACE™ Global Financial Security Index (Feb 2026).
Technical Breakdown: Lattice-Based Cryptography vs. Legacy Models
The 2026 standard for financial security has shifted from Number Theory to Lattice-Based Geometry. Algorithms like ML-KEM (Kyber) and ML-DSA (Dilithium) rely on finding the shortest vector in a high-dimensional lattice—a task that remains computationally infeasible even for quantum systems.
| Feature | Legacy (RSA-2048) | Post-Quantum (ML-KEM) |
|---|---|---|
| Quantum Security | None (Vulnerable) | Information-Theoretic Safe |
| Key Size | 256 Bytes | 1,184 Bytes (75% Increase) |
| Computational Load | Low | Medium (Optimized for 2026 Chips) |
| Regulatory Status | Phasing Out (2026-2030) | NIST/DORA Mandatory |
Strategic Implementation: The “Crypto-Agility” Framework
Financial institutions cannot simply “switch off” old encryption. The 2026 strategy is built on Crypto-Agility: the ability to update cryptographic algorithms through software configuration without overhauling hardware. This is essential for protecting long-term data such as AI-driven personal loan records and cybersecurity insurance policies.
The 3-Phase Migration Roadmap
- Phase 1: Discovery (Q1 2026) – Auditing all legacy RSA/ECC touchpoints in the payment gateway.
- Phase 2: Hybrid Deployment (Q2-Q3 2026) – Wrapping classical TLS traffic in a PQC layer to provide defense-in-depth.
- Phase 3: Native PQC (2027 onwards) – Transitioning to pure lattice-based signatures for all new digital contracts.
“In 2026, the question is no longer IF your data will be exposed to a quantum computer, but WHETHER you have implemented the mathematical armor to survive the decryption wave.”
The Future of Trust
As KOLAACE™ continues to track the convergence of AI and Quantum Computing, we predict that “Quantum-Safe” will become the new “SSL-Certified” for consumer confidence. Banks that prioritize this transition now will be the only ones capable of guaranteeing data sovereignty in the 2030s.